Configuration files in software applications
If you need configurable or changeable settings in your application, you cannot always rely on databases. In this article, I discuss various text formats for storing configuration settings for applications. Continue reading →
Ruby: setting up the development environment
Set up a Ruby development environment for your first steps with the Ruby on Rails web framework in just a few minutes. Continue reading →
DevOps Days Medellin 2024
Estupidences Continuas: Mitos de DevOps ¡Aprende a través del software! Mejora tu desempeño reflexionando sobre tu liderazgo. En este taller, desarrollará acciones concretas y adoptará hábitos de empoderamiento y un marco para gerentes de proyectos de software. ¡La casa proporciona…
Modern Times
DevOps has been on everyone’s lips for many years, but there are still numerous myths and misinterpretations. Something well-intentioned can quickly turn into an own goal. Continue reading →
Working with textfiles on the Linux shell
The command line is a powerful tool under Linux. In this article, you will learn about various little helpers for dealing with text files. Continue reading →
Test First?
Do we really have to start with the test first and then write the corresponding implementation? I think there is another way, because many roads lead to Rome. Continue reading →
Goodbye privacy, goodbye liberty
The new terms of conditions for Microsoft services released on October 2023 caused an outcry in the IT world. The reason was a paragraph who said, that now all Microsoft Services are powered by artificial intelligence. This A. I. supposed…
JCON world 2023
Continuous Stupidities – Myths of DevOps Even if it used to be called configuration management, it does not mean that the old problems have been eliminated with the beautiful new name DevOps. Due to the increasing complexity of projects and…
README – how to
README files are text files and are formatted in markdown notation. The code hosting portal GitHub, uses README files to provide useful information as a home page for project. Continue reading →
The dark side of artificial intelligence
Should we be afraid of A.I. or are the warnings from well-known A.I. researchers rather unfounded? Continue reading →
Latest won’t always be greatest
For more than a decade, it has been widely accepted that computer systems should be kept up to date. Those who regularly install updates reduce the risk of having security gaps on their computer that could be misused. Always in…
Conway’s law
Because the design which occurs first is almost never the best possible, the prevailing system concept may need to change. Therefore, flexibility of organization is important to effective design. Continue reading →
The spectre of artificial intelligence
The hype surrounding artificial intelligence has been going on for several years. Currently, companies like OpenAI are causing quite a stir with freely accessible neural networks like ChatGPT. Users are fascinated by the possibilities and some intellectual figures of our…
JPoint Moscow 2023
Test Driven: from zero to hero In the software industry, it is a common agreement that the code base has sufficient test automation. Because this is necessary for a stable DevOps process and secure refactoring. But the reality is completely…
Date vs. Boolean
Modeling database tables can quickly lead to redundancies that can easily be avoided. An example of optimized database design is the use of Date instead of Boolean. Continue reading →
Working with JSON in Java RESTful Services using Jackson
JSON is used in RESTful Services to exchange information. This article describes how Java Persistence Objects can easily transformed into JSON to use it in REST API calls. Continue reading →
jConf Peru 2022
Rolling Stones on stage: release me Everyone does it, some even several times a day. But few are aware of the complex interlocking mechanisms that make up a complete software release. This is why it sometimes happens that a package…
JVM Columbia 2022
Excepciones Tragadas El manejo de excepciones debe ser un conocimiento básico para los desarrolladores de Java. Pero un uso seguro no es tan fácil como parece en un primer momento. También varios libros recomiendan no usar excepciones para evitar problemas…
Expressions for Source Control Management Systems
Source code repositories growing over time. With multiple daily revisions by different team members, it becomes very difficult to identify important changes in the source code. Expressions in SCM enable the writing of clear, standardized commit messages that are both…
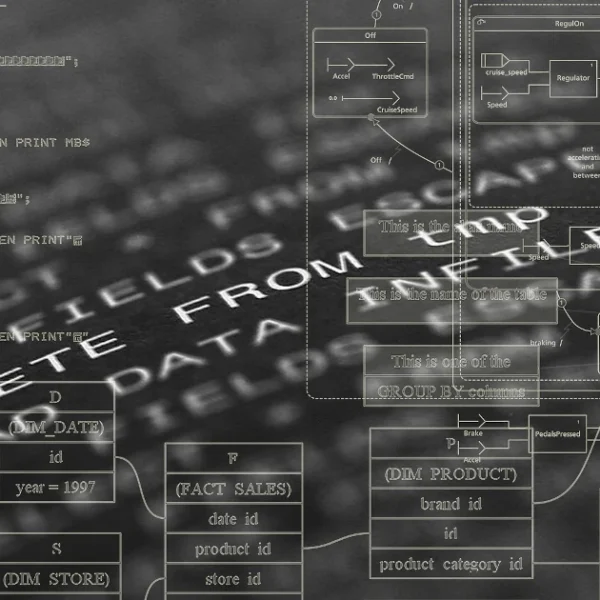
Preventing SQL Injections in Java with JPA and Hibernate
Preventing SQL Injections in Java using SQL Parameters with the Java Persistence API (JPA) and Hibernate ORM. Continue reading →
A briefly overview to Java frameworks
An important advantage of the Java platform is the large variety of freely available infrastructure components, tools and 3rd party libraries. You can quickly lose track of it. This article lists the most important Java frameworks and explains what they…
How to reduce the size of a PDF document
When you own a big collection of PDF files the used storage space can increasing quite high. Sometimes I own PDF documents with more than 100 MB. Well nowadays this storage capacities are not a big issue. But if you…
Treasure chest – Part 2
The second article of the application configuration explain implementation details and show how the demonstrated solution can be extended. It also links to the ready to use java implementation inside TP-CORE. Continue reading →
Treasure chest – Part 1
Changeable configuration for applications usually miss a history of the configuration values, wich often leads during updates to misconfigurations. The solution described in this article use a database table where configuration entry supports default and user values. Another important feature…
Backup and Transfer your Thunderbird Profile to another Computer
System backups are a very essential procedure every user need to run regular. One of the most important points of a backup is to save your full e-mail profile. In this short tutorial we show how to backup and restore…
Network spy protection with AdGuard Home on a Raspberry Pi & Docker
In this short tutorial I describe how you are able to setup AdGuard Home on and Raspberry PI 4 with Ubuntu Server and Docker, to protect your personal network against spam and spyware. Continue reading →
The Bug Fix Bingo
Nobody wants to be the one. That’s nothing new. That’s why meetings aren’t exactly popular with test engineers. To avoid despair, we recommend BugFix Bingo. Continue reading →
jConf Peru 2021 [1]
Maven POM demystified: enhance your build Since more than a decade Apache Maven is one of the most convenient Build and Reporting tools for Java projects. The success of this tool is quit more than just being a build tool.…
Installing NextCloud with Docker on a Linux Server
On our first LiveStream we explain shortly what is Docker and how fast it can installed on an Ubuntu server. After this you get an overview about all the components we need for a full NextCloud installation. Step by step…
Learn to walk with Docker and PostgreSQL
After some years the virtualization tool Docker proofed it’s importance for the software industry. Usually when you hear something about virtualization you may could think this is something for DevOps or administrators and will not effect me as a developer…
API 4 Future
APIs, or interface descriptions, are especially important in RESTful services. To keep the project well-structured from the very beginning, allowing it to grow organically while remaining maintainable, a few simple rules should be followed. This article describes them. Continue reading…
Tooltime: SCM-Manager
This article introduces a new tool for the DevOps CI /CD pipeline. The SCM-Manager can host Git, Subversion, and Mercurial repositories in one solution. Continue reading →
{j}DD Poland 2021
Refactoring Disasters: A Story how I failed For my small Open Source project TP-CORE, you can find it on GitHub, I had the gorgeous Idea to replace the iText library for OpenPDF. After I made a plan how I could…
BarCamp República Dominicana 2021
API4Future: A journey how to create a stable API By experience, enterprise applications have a long lifetime period. This is one oft the reasons why we need to pay a lot of attention for maintenance. But how we are able…
jConf Peru 2021 [2]
Mission accomplished: deploy to Maven Central Many developers have ideas they work on it in their spare time. The most of us are convinced about open source and share their own projects on platforms like GitHub. But what happen after…
JConf Mexico 2020
Continuous Stupidities – did DevOps fail? Heavy motivation to automate everything, even the automation itself, is the common understanding of the most DevOps teams. A strong dominance of administrators in those teams (Operations), transform ideas of increasing the development process…
Version Number Anti-Patterns
After the gang of four (GOF) Erich Gamma, Richard Helm, Ralph Johnson, and John Vlissides published the book, Design Patterns: Elements of Reusable Object-Oriented Software, learning how to describe problems and solutions became popular in almost every field in software…
Non-Functional Requirements: Quality
To meet the definition of code quality, it’s not enough to focus solely on the source code. Structure, organization, and maintenance also play an important role. Continue reading →
Acceptance Tests in Java With JGiven
In a standard set-up for Java projects like NetBeans, Maven, and JUnit, it is not that difficult to produce your first test code. Besides, this approach is used in Test Driven Development (TDD) and exists in other technologies like Behavioral…
Docker Basics in less than 10 minutes
A short video introduction to Docker, a Linux-based container technology for virtualizing critical applications and infrastructure services. An essential tool for developers, DevOps, and system administrators. Continue reading →
The new Java Release Cycle
When Oracle in 2017 introduced the new release cycle for Java I started to have a look for options. One of the options I can recommend is Java OpenJdk. Check in this post why I’m not agree with the new…
Apache License 2.0
Apache LicenseVersion 2.0, January 2004http://www.apache.org/licenses/ TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION 1. Definitions. “License” shall mean the terms and conditions for use, reproduction, and distribution as defined by Sections 1 through 9 of this document. “Licensor” shall mean…

























![jConf Peru 2021 [1]](https://elmar-dott.com/wp-content/uploads/2021-jConfPeru-Maven-POM.webp)






![jConf Peru 2021 [2]](https://elmar-dott.com/wp-content/uploads/2021-JCONF-Peru-Deploy-MVN-Central.webp)





