The object-oriented programming language Java was designed by James Gosling. The first version was released in 1995 by Sun Microsystems. After Oracle acquired Sun Microsystems in 2010, Java became part of Oracle’s product portfolio.
last changed:
The Java Series

- Java 21 LTS
- Java 20
- Java 19
- Java 18
- Java 17 LTS
- Java 16
- Java 15
- Java 14
- Java 13
- Java 12
- Java 11 LTS
- Java 10
- Java 9
- Java 8
- Java 7
- Java 6
- Java 5 / J5SE
- Java 1.4
- Java 1.3
- Java 1.2 / Java2
To run Java programs on your computer, you need a virtual machine (JVM). The download for this JVM is called the JRE (Java Runtime Environment). If you want to develop in the Java programming language yourself, you need the corresponding compiler, which is known by the general term SDK (Software Development Kit) or, more specifically, JDK (Java Development Kit). The JDK naturally includes the corresponding runtime environment (the JVM).
With the release of Java 9 in September 2017, Oracle announced a six-month release cycle for future Java versions. This means a new version of the popular programming language is released every year in March and September. But don’t worry, it’s not necessary to follow Oracle’s licensing terms and update your own Java version on this cycle. To provide companies with sufficient stability for their IT infrastructure, every sixth Java release is a so-called LTS (Long Term Support) and has a lifespan of three years from its release date. I have already published a more detailed article on this topic.
With the frequent release cycle, each new Java version naturally brings several new key features to the core language. It’s easy to lose track of everything. Therefore, I’ve compiled a brief overview. For those who would also like an overview of the individual Java Enterprise versions, I recommend my corresponding article on Java EE.
Version overview
To avoid getting bogged down in details, I’ll start with version 1.2, also known as Java 2, which was released in 1998. The most important features of Java 2 were the graphical Swing API and the introduction of the Just-In-Time (JIT) compiler.
In 2000, version 1.3 was released, featuring JNDI (Java Naming and Directory Interface) and JPDA (Java Platform Debugger Architecture).
Just two years later, in 2002, version 1.4 was released, expanding the available standard library with features such as regular expressions, a logging API, an integrated XML & XSLT processor, an Image I/O API, and New I/O.
With the release of version 1.5 in 2004, the version numbering system changed. Java is now numbered as a major version, meaning that from then on, it’s referred to as Java5. Just like version 1.2, the Java 5 Standard Edition (SE), or J5SE for short, brings a host of changes for everyday development. These include: autoboxing/unboxing, annotations, enums, and generics.
Released in 2006, Java6 SE extended XML functionality with the StAX parser, introduced JAX-WS for web services, and brought scripting language support, enabling scripting languages like JavaScript to run on the JVM. The most important examples are the two JVM languages Kotlin (2011, JetBrains) and Scala (2004).
Five years later, and for the first time under Oracle’s direction, Java7 SE was released in 2011. This Java release introduced the diamond operator <>. Further measures to simplify the language and increase expressiveness included simplifying the declaration of varargs methods and enabling the use of strings in switch statements. The concerns that exceptions are slow and should be used sparingly were also addressed, and exception handling was improved.
// Diamond Operator
List<String> myList = new ArrayList<>();
// varargs (variable-length arguments)
public void myMethod(String... args);Java8 SE took another significant step forward with its release in 2014. In this release, Oracle provided the Java community with long-awaited features such as lambda functions and the Stream API, to name just a few of the most important new features. Furthermore, the Date & Time API was completely redesigned, with changes inspired by the then widely used JODA-Time library.
// ForEach Lambda
myList.forEach(element -> System.out.println(element));
//Stream API
myList.stream()
.filter(element -> element.startsWith("A"))
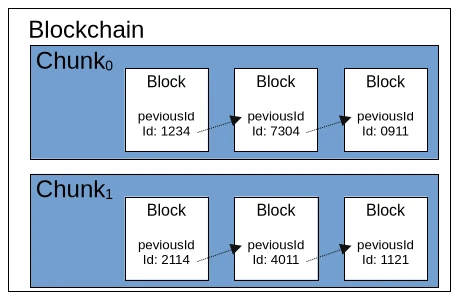
.forEach(System.out.println); The 2017 release of Java9 SE marked a turning point. Due to the introduction of the module system, the entire standard library was reworked so that the individual APIs were no longer bundled into a single, gigantic JAR file. The resulting modules now required less memory. These massive changes demanded enormous effort from many long-standing projects to migrate to the new Java version. Furthermore, Java 9 introduced the Java Shell, or JShell for short, a command-line tool that allows Java functions to be executed as scripts.
// module-info.java
module com.example.myapp {
requires java.base;
exports com.example.myapp;
}Further significant changes were brought with the release of Java10 SE, which was released just a few months after Java 9 in 2018 and necessitated additional migration efforts. This release introduced the Local Variable Type interface with its associated keyword var. Furthermore, Release 10 also marked the start of Time-Based Versioning for the Java language. A new major version is released every six months, typically in March and September. An LTS (Long Term Support) version is released every three years.
// the var KeyWord
public static void main(String[] args) {
var message = "Hello World, Java10!";
System.out.println(message);
}The first Long Term Support version for Java was released in the fall of 2018. Release Java11 carries the LTS designation and receives updates for three years. Due to the short release cycles, this version contains only a few API changes. The String class, in particular, received many new methods designed to simplify working with strings.
// String FUnctions
String text = new String(" Helle Java 11 LTS world! ");
text.strip();
text.isBlank();
text.lines().count();The most important change in the Java12 SE release, released in spring 2019, besides several API extensions, is the ability to use expressions in switch statements.
// switch expressions
Var day = 1;
String weekday = switch(day) {
default -> "";
case 1 -> "Monday";
case 2 -> "Tuesday";
...
}Java13 SE was released as planned in autumn 2019 and improved expressions in switch statements. It also introduced text blocks, which eliminate the need for resource-intensive string concatenations.
// textblock
String text = """
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do
eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim
ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut
aliquip ex ea commodo consequat. Duis aute irure dolor in
reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla
pariatur. Excepteur sint occaecat cupidatat non proident, sunt in
culpa qui officia deserunt mollit anim id est laborum.
""";With the release of Java14 SE in March 2020, records were introduced. These data structures are intended to make code more compact and readable, as getters and setters no longer need to be defined.
// records
public record Person (String name, String address) {}The release of Java15 SE, released in autumn 2020, standardized text blocks and introduced sealed classes. Sealed means that a class cannot be inherited.
// inheritance protection
public sealed class Shape permits Circle {
// Class body
}
public final class Circle extends Shape {
// Class body
}In 2021, the release of Java16 SE standardized various features, including sealed classes, pattern matching for instanceof, and records.
// Pattern Matching instanceof with auto cast
if (obj instanceof String s) {
System.out.println(s);
}Java17 SE LTS was released as planned in autumn 2021, replacing Java 11 SE LTS after three years. In this version, the Java Applet API and the Security Manager were marked as deprecated.
Java18 SE established UTF-8 as the default code page for the JVM. The Vector API was also introduced with an experimental status.
// Java Vector API
import jdk.incubator.vector.*;
import java.util.Random;
public class VectorExample {
// Use preferred vector species for optimal CPU performance
static final VectorSpecies<Float> SPECIES = FloatVector.SPECIES_PREFERRED;
// Vectorized implementation using the Vector API
static void sqrtsumVector(float[] a, float[] b, float[] c) {
int i = 0;
int upperBound = SPECIES.loopBound(a.length); // Efficient loop bound
// Process data in chunks matching the vector length
for (; i < upperBound; i += SPECIES.length()) {
var va = FloatVector.fromArray(SPECIES, a, i);
var vb = FloatVector.fromArray(SPECIES, b, i);
var vc = va.mul(va) // a[i]²
.add(vb.mul(vb)) // + b[i]²
.neg(); // - (a[i]² + b[i]²)
vc.intoArray(c, i); // Store result
}
// Handle remaining elements (tail case) with scalar loop
for (; i < a.length; ++i) {
c[i] = -(a[i] * a[i] + b[i] * b[i]);
}
}
} Released at the end of 2022, Java19 SE included several optimizations and integrated the Loom project to enable virtual threads. The Foreign Function & Memory API was also incorporated into the JVM.
// Natice C Memory allocation & Slicing in Java
Arena arena = Arena.ofAuto();
MemorySegment memorySegment = arena.allocate(12);
MemorySegment segment1 = memorySegment.asSlice(0, 4);
MemorySegment segment2 = memorySegment.asSlice(4, 4);
MemorySegment segment3 = memorySegment.asSlice(8, 4);
VarHandle intHandle = ValueLayout.JAVA_INT.varHandle();
intHandle.set(segment1, 0, Integer.MIN_VALUE);
intHandle.set(segment2, 0, 0);
intHandle.set(segment3, 0, Integer.MAX_VALUE);Java20 SE, released as usual in the spring of 2023, didn’t introduce any new features but focused on stabilizing existing ones.
In the fall of 2023, Java21 SE LTS, a Long Term Support version, was released. This release finalized Virtual Threads.
public class VirtualThreadsExample {
public static void main(String[] args) throws
InterruptedException {
var executor =
Executors.newVirtualThreadPerTaskExecutor();
executor.submit( () ->
System.out.println("Running in virtual thread"));
executor.submit( () ->
System.out.println("Running another virtual thread"));
Thread.sleep(1000);
complete
}
}

![jConf Peru 2021 [2]](https://elmar-dott.com/wp-content/uploads/2021-JCONF-Peru-Deploy-MVN-Central.webp)